WRITTEN BY: Thomas Forrister
As computer networks extend and intensify the reach of technology into human lives increasingly, we become more dependent on the presence and trustworthiness of those networks. One of the particularly insidious security threats is denial of service, and especially distributed denial of service. The challenge is that with the increasing number of types of devices on the networks the opportunities to recruit vast networks of devices into botnets is also growing with a flourishing industry in selling the attack services of these networks. Most likely driven by the financial opportunities, there is also evolving creativity in the nature of the attacks. The most prevalent approach to such attacks is understanding the nature of each attack as it unfolds and disable it. In order to do this, the attack must occur and then be analyzed.
Dr. Karen Sollins and her students are focusing on the question of how to take a systematic approach to reducing opportunities for distributed denial of service attacks. Their work is based on the observation that a denial of service attack is an attack on one or a set of vulnerable and critical resources in order to disable the victim. If one can transform the situation so that resource exhaustion is either disabled or redesigned to be non-critical, then not only will a particular attack be disabled, but all attacks on the resources be eliminated. It is expected that this approach allows for a priori mitigation of whole classes of attacks.
In this early stage of the research project, specific classes of resources are identified and analyzed for their vulnerabilities. Presently, Sollins and her team are examining three qualitatively different types of resource exhaustion: routing in mobile ad-hoc networks, protocol translation for very low-capacity edge (IoT) devices, and general volumetric flooding attacks. These are intentionally chosen to allow us not only to consider various important scenarios, but also to challenge us to think more broadly about the question of how to design network protocols to be more resilient to these kinds of vulnerabilities.
The mobile ad-hoc networking scenario is driven by, but not limited to, military deployment contexts in which suites of humans and various kinds of devices are deployed in the field and by necessity both ad-hoc and mobile. Devices might include the soldiers, trucks and other terrestrial vehicles, and perhaps airborne drones. The scenario could easily be transformed into civilian situations as well. One of the key challenges in such a domain is providing confidence that traffic will be delivered from source to destination as the routes are changing. Therefore, the team is focusing on the routing protocols used to determine valid paths for the traffic under dynamically changing conditions. Denial of service attacks on the routing may take several forms; consider corruption of information, for one. Corruption itself may take several forms. The nodes in the network exchange information about how to reach other nodes through themselves. This may be changed to recommend much longer or invalid paths. In another form of attack, it may be changed to lead all traffic to a single “victim” node, overloading it with unintended traffic. In a third form of attack, it may cause all traffic to be delivered to a malicious node. The situation is that there is no one perfect routing protocol but several leading alternatives with differing advantages and disadvantages. In particular, one design choice is whether to only update routing information at a specific node for a particular destination on demand when a packet arrives to be forwarded toward its destination, or to precompute new routes as the topology changes. These have very different performance behaviors under differing types of loads and differing denial of service vulnerabilities more generally. This component of our research examines the attack vulnerabilities of these differing types of routing protocols.
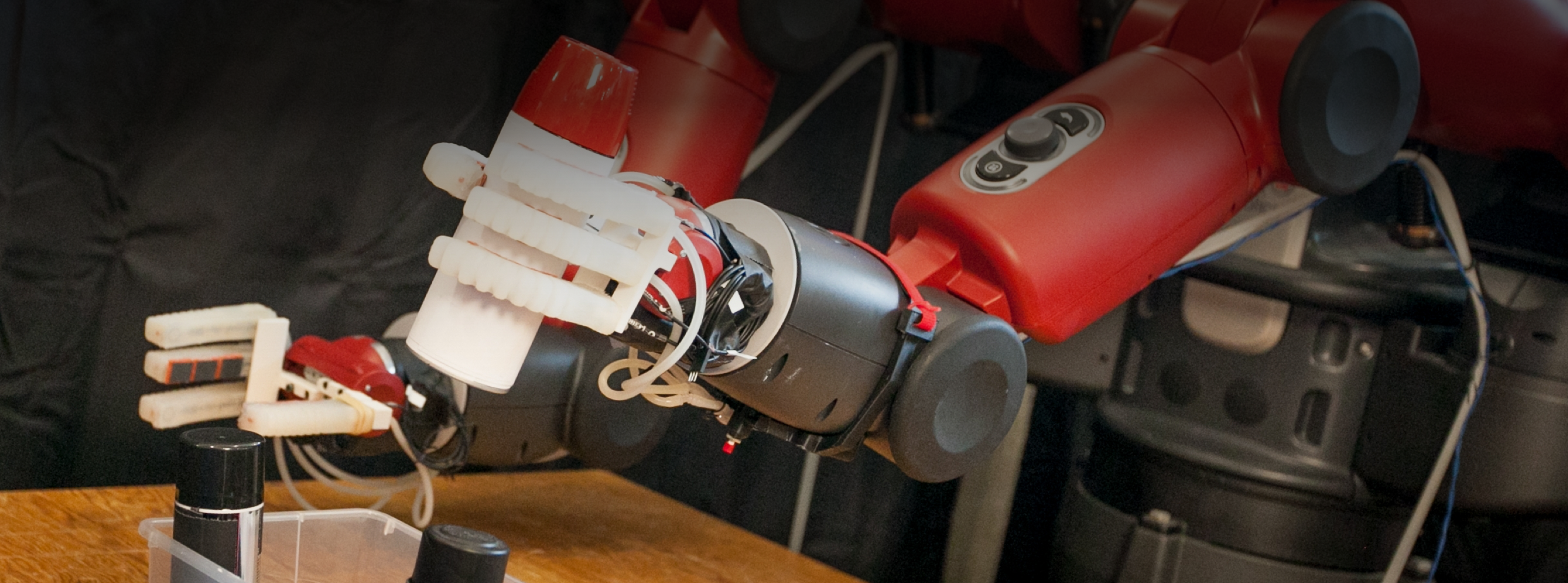
A second scenario that presents a very different type of vulnerability can be found in the IoT domain. In this component of the research, the team is considering particularly low-capacity edge devices, noting from their previous research that such low-capacity devices running one of the particularly low-capacity networking technologies (e.g. 802.15.4, BLE, or Zigbee) prevent the edge devices from supporting a full TCP/IP stack, and especially the security protocols that require certificate or key exchange. These communication protocols support only extremely small packets, which also eliminates the possibility of using IP addresses, especially IPv6 addresses. As a result, the edge devices are generally designed to communicate with a protocol translator, likely a concentrator for a set of such devices, which provides the “end point” for Internet wide communication for accessing remote services and capabilities. This particular component of our research concentrates on the vulnerable resources necessary to manage protocol translation between suites of IoT devices and Internet-based services. Here the team analyzes the various tasks and responsibilities of the translator and to date have identified several demonstrable bottleneck vulnerabilities, including the structure required for mapping edge-to-translator connections and translator-remote-service connections, and outgoing socket management in the translator. They have demonstrations of exhaustion of both of these based on a variety of types of attacks. One is an attack on table capacity and possibly memory, and the other on the network interface subsystem. Sollins and her team are working on systematic approaches to redesign to mitigate the whole classes of attacks on these resources.
The third category of vulnerability derives specifically from volumetric attacks in the Internet. One of the most common types of volumetric attacks is on the initial packet (the SYN packet) used to set up a TCP connection. Each initial SYN packet leads to setting up the receiver side of a connection, requiring a saved state. In this case, we initially identify several resources being exhausted, including network bandwidth either in the network itself or at the destination victim, state within the victim, or computational resources required for the victim to handle the flood. There is a widely used approach to protecting state in the memory of the victim, known as SYN cookies, in which the potential victim does not store state initially, thus avoiding creating massive amounts of malicious state, but at the cost of computing and signing the state and returning it to be returned in follow-up messages. The tradeoff is that the victim now may exhaust its computational resources for each such attack packet. In their research, Sollins and her team are studying alternatives to systematically “push back” on potential attackers without significantly increasing the burden on valid customers. It is important to note that the valid customers may not even be using TCP, but rather alternatives. Thus, this work is studying the resource sensitivity among different protocols.
“Stepping back from this work, it is our objective in the longer run to gain a broader understanding of the vulnerabilities of different types of resources important to the overall operation of networks and network protocols,” says Sollins. Their long-term objective is to understand the types of critical and exhaustible resources important at different layers of the network protocol stack. Furthermore, the team strives to gain an understanding of which resources present what vulnerabilities, to allow for designing protocols to reduce or eliminate whole categories of such attacks.